1.12 Explain virtualization fundamentals (virtual machines)
Everything we talked about so far involves physical hardware. But organizations are moving to virtual hardware.
Cisco’s server offering is called the Cisco Unified Computing System (UCS). There are many UCS models available, including blade servers and rack servers. You might buy servers from another vendor such as HP, Dell, or Lenovo.
Consider an organization that has four servers: a web server, a database server, an e-mail server, and a file server. That’s four physical servers that must be powered on, configured, maintained, and connected to the network. Each server may only be used at 10% or 20% of its capacity. What can we do to make our infrastructure more efficient?
We get rid of the servers and set up a single physical server. We install an application on this server called a hypervisor. The hypervisor allows us to create multiple “virtual” servers on the same physical server. We install a server operating system on each virtual server. These are known as Virtual Machines or VMs. Each virtual server’s operating system talks to the hypervisor, and the hypervisor talks to the server’s physical hardware. The operating system doesn’t know that it’s running on a hypervisor; it thinks that it is running on a physical server.
The advantage is that we can reduce the number of physical server devices required – this reduces maintenance costs, power consumption, and the number of servers required.
Common hypervisors include VMWare and Microsoft Hyper-V (which is included with Windows Server operating systems).
Each virtual server thinks it has its own RAM, hard disk space, and processor. The hypervisor figures out how to proportion the hardware to meet the needs of each VM. But what happens when the physical server has only one physical network connection and all the VMs need to share it? And what happens when the different VMs need to talk to each other?
We create a virtual NIC (Network Interface Card) that connects to each VM. The hypervisor sees traffic from each VM and sends it out the physical server’s network interface. The physical server’s network interface also receives traffic destined for the VMs, which the hypervisor forwards appropriately.
We can also create a virtual switch, virtual router, and virtual firewall inside the hypervisor. Each virtual NIC connects to the virtual switch. These virtual devices communicate with each other using the same concepts as their physical counterparts, but all forwarding decisions are made by the software of the hypervisor.
We can set up a virtual Cisco switch like a Cisco Nexus virtual switch, which runs the Cisco switch operating system inside a software application. The benefit of installing a virtual Cisco switch inside a hypervisor is that we can configure it the same way as with a physical switch.
A virtual network has the same vulnerabilities as a physical network because the physical hardware does not provide any protection. Some of the problems include
- Traffic that moves from one virtual machine to another is entirely inside the physical host device and cannot be monitored by external security devices
- Virtual machines may have direct access to the internet
- A user on one virtual machine may be able to access other virtual machines on the same virtual network
- A virtual machine may have access to network resources on the physical network
- A user with access to the physical machine’s hard disk drive can move a virtual machine to another physical machine
- It is easy to create or destroy an unauthorized virtual machine without being detected
A virtual firewall monitors traffic produced by the virtual machines. When operating in bridge mode, a virtual firewall operates exactly like a physical firewall, as part of the network infrastructure. When operating in hypervisor mode, the virtual firewall exists on a higher layer in the hypervisor. It monitors all virtual machine activity, but none of the VMs can see it. A hypervisor mode firewall is better because it cannot be seen or modified by users who only have access to the virtual environment.
In an organization that maintains physical servers, if a user or department needs a new server, they must place a procurement request and justify the expense. The IT department would purchase a physical server, install it, set it up, connect it to the network, and configure it.
In a VM setup, the IT department maintains several large physical servers with spare capacity. When a user or department needs a new a server, they must still place a procurement request. The IT department sets up a virtual machine on one of the physical servers, meeting the specifications requested by the department. The IT department may bill the other department for the use of the virtual server.
If we take virtualization one step further, we have a cloud.
A defining characteristic of the cloud is on-demand self-service. Any authorized user can log in to the cloud and create a virtual server without having to go through the IT department. The cloud automatically creates the VM without any of the users having to worry about the underlying physical hardware. If a physical server begins to fail, the cloud moves the VM to another physical machine. The cloud software also creates the virtual networking hardware and connects it. A user can stop and start the cloud server any time they want.
The cloud also offers resource pooling. That means that the cloud does not allocate any specific hardware to any specific virtual machine. All the physical components of the cloud are allocated to all the virtual machines. The cloud automatically allocates any necessary physical component to any virtual machine that requires it.
Rapid elasticity allows the cloud to grow or shrink almost instantly in response to user demand. For example, if we need ten new servers, we can have them up in a matter of minutes.
A cloud service is available over the internet from many types of internet connections and locations. This is known as broad network access.
The cloud also provides a measured service. That means that we can monitor how much use we the cloud. In many cloud services, the use of a virtual server is billed per hour, and the hourly rate depends on the operating system and type of hardware.
The two major public cloud service providers are Amazon Web Services (AWS) and Microsoft Azure. A public cloud is available to anybody. AWS and Azure offer many types of cloud services, not just servers. Cloud services include e-mail marketing, DNS, and artificial intelligence.
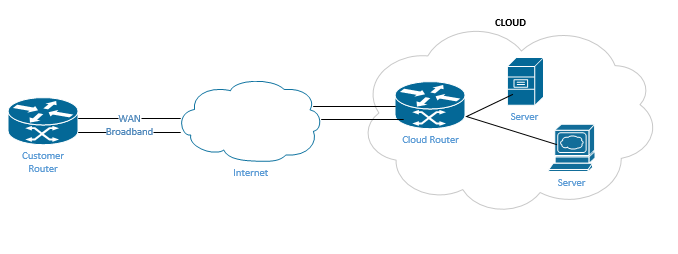
When we subscribe to a public cloud service, we can connect our network to it via a WAN or VPN. Then the cloud resources appear like they are physically connected to our local network.
If we don’t want to outsource our cloud services, we can build our own private cloud. It is quite difficult to build a true private cloud that can provide on-demand self-service and rapid elasticity. A large organization may consider a private cloud if they have a substantial number of server resources that they can pool together, or the physical security requirements justify it. For example, a city can pool the servers from its public works department, police department, and fire department to create a private cloud.
The cloud service provider must create a catalog, which lists all the products that it offers. Connected to each product inside the catalog is a workflow or script that automatically generates the underlying system. For example, if I offer a server with the Windows Server 2019 operating system in my catalog, the work flow might be as follows
- Locate a physical server in the cloud that has available resources
- Allocate the correct amount of physical resources (hard disk drive, RAM, processor) for the new virtual machine
- Create a new virtual machine on the physical server
- Install the operating system on the virtual machine
- Configure the virtual machine with a username, password, hostname, etc.
- Create a virtual network adapter on the virtual machine and connect it to the virtual switch
- Assign the virtual network adapter an IP address
The workflow must accomplish these tasks by communicating with the virtual machine software via an API, or Application Programming Interface. That means that the VM software publisher creates a connector (called an API) in its software to allow requests from automated scripts in addition to human interaction.
The cloud appears to work seamlessly, but behind the cloud are many people who create, monitor and maintain it. We must watch the consumption of the cloud’s physical resources. When demand on the cloud is high, we must add more physical resources. We must also replace any physical devices that fail. It is important to ensure that the cloud’s physical resources are redundant, so that there is no single point of failure.
The cloud is not limited to hardware.
SaaS or Software as a Service is a concept where we pay for the right to use a software application. Somebody else takes care of writing the software, hosting the software, and backing up the data. Our only responsibility is to use the software. We don’t have to think about the physical hardware. Examples of SaaS include Salesforce, Microsoft Exchange Online, and Office 365. SaaS is typically billed on a per user per month basis.
IaaS or Infrastructure as a Service is a concept where we pay for the right to use different hardware components. For example, we can rent different server types from Amazon Web Services’ EC2, or we could rent DNS services from Route 53. IaaS is charged on a per device per hour (or per month) basis. For example, a large server might cost $0.35 per hour. If I buy an EC2 server it may come with a license for an operating system, such as Windows Server 2019. The cloud allows us to mix and match different hardware components so that we can build exactly the type of infrastructure that we require. IaaS allows us to pay for only what we use. If we use a server for five hours, we pay for five hours.
PaaS or Platform as a Service is a hybrid between the SaaS and IaaS. In PaaS, we don’t have to worry about the hardware. We simply upload the applications we want, and the cloud provisions the necessary hardware to run them. We are still responsible for configuring the applications and backing up their data. An example is Amazon Hadoop. PaaS is typically billed on a per hour per resource basis. For example, we could be billed for each GB of data we store each month, or we could be billed for processing capacity we use. We can reduce our costs by using more efficient applications.
A PaaS may also offer software development tools so that we can write code inside the cloud and automatically have it executed.
We can connect to the cloud via the internet. For many SaaS applications, connecting to the cloud via the internet is great. For example, accessing Salesforce or Office 365 over a direct internet connection allows users to work remotely without having to use a VPN or WAN. That means that we can start using the cloud without having to worry about the internet connection or where our users are located.
Accessing the cloud via a normal internet connection can be bad because the internet does not provide any Quality of Service. Therefore, more important traffic is not prioritized. Also, the internet does not provide any encryption or authentication. For example, a server in the cloud will be accessible over the internet but won’t act like it is connected to the enterprise network.
There are several ways to create a WAN connection with our cloud
- We can create a site-to-site VPN (Virtual Private Network) connection. A VPN is like a tunnel between us and the cloud. Our data travels over a normal internet connection, but over a tunnel
- We can create a virtual router inside the cloud’s virtual network and establish a VPN back to our physical network. Cisco offers a virtual router called the Cloud Services Router or CSR.
- We can obtain an MPLS or Ethernet WAN connection. This requires cooperation between the ISP and the cloud provider. Cooperation with the larger service providers is expected, because they have many data centers in many countries. For example, AWS has data centers in Montreal, California, Oregon, Virginia, Frankfurt, and Tokyo (among others). That means that the WAN service provider can find a nearby connection back to the cloud, no matter where the customer is located.
A WAN has better security than an internet connection. It also provides Quality of Service. But a WAN is more expensive than a normal internet connection. Prior to purchasing a WAN, we should think about the speed and capacity that we need.
An Intercloud Exchange is a WAN connection between one service provider and another. We might choose to move our cloud services from one cloud provider to another. Or we might purchase some services from one service provider and other services from another service provider. For example, we might purchase Office 365 and Active Directory from Microsoft Azure Active, because no other service provider can offer it. We might purchase database servers from AWS, because they are cheaper. Then we connect both services together.
In many setups, we install a broadband internet connection and a WAN connection. A broadband connection is cheaper and has a higher capacity.
Traffic that can travel over a broadband internet connection goes over the broadband, and the rest of the traffic goes over the WAN.