2.10 Given a scenario, install and configure browsers and relevant security settings
- Browser Download / Installation
- Trusted Sources
- Hashing
- Untrusted Sources
- Trusted Sources
- Extensions and Plug Ins
- Trusted Sources
- Untrusted Sources
- Password Managers
- Secure Connections / Sites – Valid Certificates
- Settings
- Pop Up Blocker
- Clearing Browsing Data
- Clearing Cache
- Private Browsing Mode
- Sign in / Browser Data Synchronization
- Ad Blockers
Browser Download / Installation
Since many applications and tools are now delivered through the cloud (as a service!), most of what we do happens through a web browser or at least over the internet. We must take care to ensure that our access is secure.
- Download web browsers, plugins, and other applications from a trusted source (the publisher’s official website). Other sites may offer a free download of the same browser, but it is likely bundled with adware.
- Check the file hash. A hash is a digital fingerprint of the file that you are downloading. A reputable publisher will list a file hash for each application available for download. Compare the hash in the file that you downloaded with the hash on the website. If they aren’t the same, then the file has been modified.
- Check the digital signature. A reputable publisher will digitally sign applications that they distribute. If the digital signature is not valid, then the file is not legitimate.
Password Manager
I was opposed to password managers. Why should I give somebody else control of my passwords? But now I need to keep track of hundreds of passwords.
It is a bad idea to use the same password on multiple sites – if one site suffers a data breach, then all my accounts will be compromised. But I can’t possibly remember all the passwords. Writing down a bunch of passwords is also not a good option.
The password manager does the following
- Randomly generates a secure password for each new site that you sign up at
- Stores the username and password combination for each account (and updates them when they change)
- Automatically enters the username and password combination when you sign in to a website
How to choose a password manager
- Find a password manager that stores all your passwords on your local computer.
- The password manager should encrypt all your passwords with a master password and should support two factor authentication.
You should use two factor authentication for any account that supports it.
Secure Connections / Sites – Valid Certificates
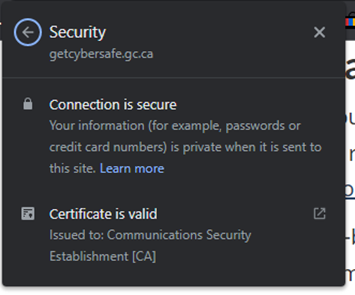
When you visit a website, make sure that it has a valid SSL certificate. You can verify that a website is secure by looking for a padlock icon in the address bar.
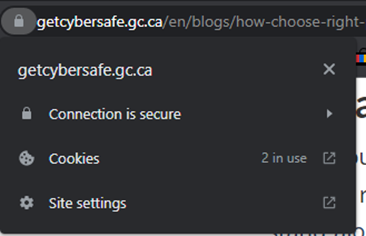
The padlock just tells you that the website encrypts traffic between you and the server. Anybody can set up a website and install a certificate in a matter of hours. You should verify that you are on the correct website, and that the certificate is issued to the organization that owns the website.
Settings
Some settings that we should consider changing.
- Pop Up Blocker. A pop-up blocker blocks pop ups. Some pop ups are legitimate, so you must train the blocker to allow some sites to show pop ups.
- Ad Blocker. An ad blocker blocks advertisements, including those that are embedded into a webpage. Ad blockers are good because they reduce the ability of third parties to track your browsing habits through advertisements.
- Clearing Browsing Data and Cache. You may choose to clear your browsing data and cache after accessing a sensitive website.
- Private Browsing Mode. Private Browsing Mode prevents the web browser from saving any history or cookies. This also prevents websites from keeping track of you after multiple visits.
- Sign in / Browser Data Synchronization. Browser data synchronization allows you to share your browsing history, bookmarks, and passwords across multiple devices. This may be convenient, but it also represents a huge privacy risk. By enabling this feature, you are sharing your data with third parties.
