1.5 Explain common ports and protocols, their application, and encrypted alternatives
- File Transfer Protocol (FTP)
- Secure Shell (SSH)
- Secure File Transfer Protocol (SFTP)
- Telnet
- Simple Main Transfer Protocol (SMTP)
- Domain Name System (DNS)
- Dynamic Host Configuration Protocol (DHCP)
- Trivial File Transfer Protocol (TFTP)
- Hypertext Transfer Protocol (HTTP)
- Post Office Protocol v3 (POP3)
- Network Time Protocol (NTP)
- Internet Message Access Protocol (IMAP)
- Simple Network Management Protocol (SNMP)
- Lightweight Directory Access Protocol (LDAP)
- Hypertext Transfer Protocol Secure (HTTPS) Secure Sockets Layer (SSL)
- HTTPS Transport Layer Security (TLS)
- Server Message Block (SMB)
- Syslog
- SMTP TLS
- Lightweight Directory Access Protocol (over SSL) (LDAPS)
- IMAP over SSL
- POP3 over SSL
- Structured Query Language (SQL) Server
- SQLnet
- MySQL
- Remote Desktop Protocol (RDP)
- Session Initiation Protocol (SIP)
- IP Protocol Types
- Internet Control Message Protocol (ICMP)
- TCP
- UDP
- Generic Routing Encapsulation (GRE)
- Internet Protocol Security (IPSec)
- Authentication Header (AH)
- Encapsulating Security Payload (ESP)
- Connectionless vs Connection-Oriented
We mentioned ports earlier. Remember that a port is a number that is attached to the end of the IP address. In this case, we aren’t talking about physical ports, but logical ports.
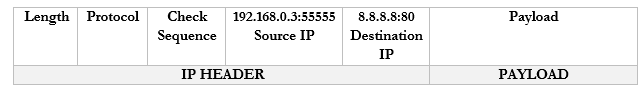
And I mentioned the example that the Google server way in California spends its whole day listening to incoming web traffic. It does so on port 80. That is, it understands that traffic sent to 8.8.8.8:80 is requesting the Google website. It might ignore other traffic, or it might listen for different types of traffic on other ports. For example, it might listen for management traffic on port 300.
Now, let’s say that I have 100 browser tabs open at the same time. I am trying to access Google, CNN, YouTube, etc.. If my computer is bombarded with traffic from all these sources at the same time, it will not know which packet goes where. So, what can it do? It adds a port to the end of each request.
For example, it sends a packet to Google.com with the port 55555 as the source. Google.com knows that it should send a reply back to 192.168.0.3:55555.
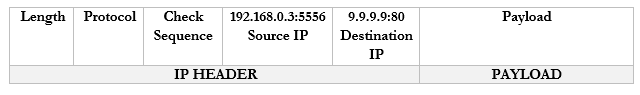
It sends a packet to CNN.com with the port 55556 as the source. CNN.com knows that it should send a reply back to 192.168.0.3:55556.
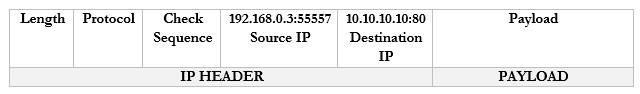
It sends a packet to YouTube.com with the port 55557 as the source. Google.com knows that it should send a reply back to 192.168.0.3:55557.
Many common protocols have ports that are reserved for them. If your computer/server is running a specific application, that application will listen for traffic on a specific port (unless you configure it to use a different, non-standard port). There are 65,535 total ports (range is from 1 to 65,535).
Let’s look at some of the most common protocols and their associated ports
| Port Number/Protocol Name | Use |
| 20 and 21/FTP and FTPS | File Transfer Protocol FTP is a protocol for transferring files between two devices FTPS adds a security layer to the file transfer. It requires that the server have an SSL certificate installed. The entire session can be encrypted or only specific portions of it. |
| 22/SSH | Secure Shell Secure Socket Shell (or Secure Shell) allows a user to connect to a remote computer. SSH authenticates the identity of the remote computer to the user and the user to the remote computer. SSH creates a tunnel between the user and the remote computer. The user will require an SSH client such as PuTTY, and the remote computer will require an SSH daemon. Each remote computer must be set up to accept SSH logins (typically over port 22). Network firewalls must be configured to allow traffic over port 22. The user’s IP address should be whitelisted on the firewall (do not allow SSH connections from any IP address) |
| 22/SFTP | SSH File Transfer SFTP is a file transfer protocol within the SSH protocol. Provided that the SSH session is secured and properly configured, then the SFTP session will be as well. |
| 23/Telnet | Telnet Telnet provides a text-based terminal to communicate with a network device or server. Telnet is like SSH but does not contain any security. It is no longer popular due to lack of security. Use SSH instead. |
| 25/SMTP or 587/SMTP over TLS | Simple Mail Transfer Protocol Used to communicate with an e-mail server (for sending e-mail only) Can be secure or insecure, depending on whether the client and server agree to encrypt data between them. SMTP with TLS can be used for encrypted communication. |
| 53/DNS | Domain Name Server Translates Domain Names/Hostnames to IP addresses (necessary to locate network resource) Consider that a human can remember text names (such as google.ca or amazon.com), but for a web browser to access a website, it must figure out the corresponding server IP address. The DNS converts human-readable domain names into machine-readable IP addresses. By default DNS is not secure, but DNS can be run over the HTTPS protocol. |
| 67/68/DHCP | Dynamic Host Configuration Protocol Allows a device to request a dynamic IP from a DHCP server. Allows a DHCP server to dynamically assign IP addresses to other devices. When a device first joins a network, it may not need an IP address and must request one. DHCP does not have a secure alternative, but with proper network security, DHCP messages can be protected. |
| 69/TFTP | Trivial File Transfer Protocol TFTP is like FTP in that it allows a user to transfer files over a network. TFTP has a simple design. An important use of TFTP is to allow a device to boot over a network. A device with no operating system can load one over the network into memory. TFTP does not have any security. |
| 80/HTTP or 443/HTTPS | Hyper Text Transfer Protocol Used to transmit web site data (insecure). The secure alternative is HTTPS HTTPS can use SSL (Secure Sockets Layer) to encrypt the data, or the newer TLS (Transport Layer Security). Both methods use port 443. |
| 110/POP or 995/POP over TLS/SSL | Post Office Protocol Allows an e-mail client like Outlook to retrieve messages from a server. With POP, the e-mail server receives messages on behalf of the user. Via POP, the e-mail client asks the server if there are any new messages. If so, the e-mail client downloads messages from the server. The server deletes the messages after they have been downloaded. POP is no longer common; it has been replaced with IMAP and Exchange, which allow an e-mail client to “sync” with a server. POP can be encrypted with TLS/SSL and run over port 995. |
| 123/NTP or NTS | Network Time Protocol NTP allows network-connected devices to sync their clocks, to within a few milliseconds of UTC. NTP can function accurately even when the network has high latency through the clock synchronization algorithm. NTP can obtain the time from a central server or from a peer. The secure version is called Network Time Security (NTS). |
| 143/IMAP or 993/IMAP | Internet Message Access Protocol Allows an e-mail client to communicate with an e-mail server. The client and server “sync” so that both have the same data (e-mails, calendar entries, contacts, etc.). If an e-mail is deleted in the e-mail client, then it is also deleted on the server. IMAP may be secure or insecure. The secure version uses TLS and port 993. |
| 161/162/SNMP | Simple Network Management Protocol Allows a user to collect and manage data about managed network devices, including routers, switches, servers, and printers. There is no secure version. |
| 389/LDAP or 636/LDAPS | Lightweight Directory Access Protocol Allows users to access different directories Directories include e-mail directories, users, phone numbers, printers, and services The secure version is called Lightweight Directory Access Protocol Secure and uses port 636. |
| 445/SMB/CIFS | Server Message Block/Common Internet File System Allows computers on a network to share files and printers There is no secure version. |
| 514/syslog | Syslog Syslog allows network devices to generate logging messages and send them to a server. This allows an administrator to remotely view logs from many different devices in a centralized location. Syslog can be secured with TLS. |
| 548/AFP | Apple Filing Protocol Allows Apple devices to share files There is no security |
| 1433/SQL Server | Structured Query Language (SQL) Server SQL is a database server developed by Microsoft. It can use TLS to encrypt the communication. |
| 1720/H.323 | H.323 Allows devices to communicate audio-visual content over a network. Used in videoconferencing applications. The communications can be encrypted. |
| 3306/MySQL | MySQL MySQL is a database server developed by Oracle (similar to SQL). It can use TLS to encrypt the communication. |
| 3389/RDP | Remote Desktop Protocol Allows a user to remotely connect to a Windows server or computer via a Graphical User Interface RDP can encrypt the communication if enabled by a user or administrator. |
| 5060/5061/SIP | Session Initiation Protocols Used for real-time communications involving VoIP and video conferencing. Also used by mobile devices for voice over LTE. Encryption is possible when there is a direct connection between the sender and the recipient (which is unlikely). |
Ports 0 to 1023 are well known ports reserved for specific applications. Only those applications should be using those ports. Ports 1024 to 49151 are registered ports. An application developer can apply to have his application use one of those ports. Ports 49152 to 65535 are called dynamic ports or ephemeral ports. An application can borrow one of those ports temporarily if it needs to communicate.
There are four main protocol types. Each protocol can fit into one of the following types.
| ICMP | Internet Control Message Protocol ICMP does not carry user traffic, only machine-to-machine communications. Network equipment use ICMP messages to communicate errors and status with each other. ICMP messages are used by ping and tracert commands for example. |
| UDP | User Datagram Protocol UDP is connectionless, unlike TCP. UDP is good for applications that do not check for errors (or that do not have time to check for errors). Remember that in a communication, the sending device breaks up the data into packets and the receiving device puts the packets back together into something meaningful. If the packets arrive out of order, the receiving device can reorder them. If they arrive damaged, the receiving device can request that they be resent. If you’re downloading a file like an Excel spreadsheet, the sender breaks it up into packets. The receiving computer puts the packets back together. What matters is that the end result makes sense. If you’re on a live video stream or VoIP phone call, the transmission is also broken into packets. Every packet must arrive in the correct order because they are being replayed in real time. If the packets for a video stream or phone call arrived in the wrong order, the call or video wouldn’t make any sense. A poor-quality connection would result in poor video transmission due to errors in the packets but attempting to resend them would be counterproductive. UDP is -Transactional (allows a query-response structure, like DNS) -Simple (useful for protocols that do not need overhead, like DHCP) -Stateless (allows many clients to receive the same connection, good for protocols like IPTV) -Lack of retransmissions (no delay caused by retransmissions of missing/incorrect data) -Multicast (can broadcast information to many clients, like in service discovery protocols) UDP is like a guy at the top of a hill yelling. He doesn’t keep track of who is listening or whether they received the message. And it’s possible for multiple people to hear him. |
| TCP | Transmission Control Protocol TCP is like a one on one conversation where each participant acknowledges every sentence said by the other participant. If one participant misheard something, it asks the other participant to repeat it. TCP involves a connection between two peers, with a three-way handshake. Each time a peer receives data, it verifies that the data has been received correctly. If not, the recipient requests that the sender retransmit the data. TCP is more reliable than UTP, but it is not useful for real-time applications because it introduces latency into the connection. The TCP Model has four layers that follow the OSI Model Link Layer (Physical and Data Link layers of OSI). TCP doesn’t worry about the link layer, because the protocol doesn’t deal with the physical link. Internet Layer (Network layer of OSI). IP Packets are created on the Internet Layer. Transport Layer (Transport layer of OSI). The transport layer moves the packets. On the transport layer, IP Packets are encapsulated inside segments. Application Layer (Session, Presentation, and Application Layers of OSI). The application layer allows programs to talk to the network. |
| IP | Internet Protocol IP transfers data packets across the internet. IP is considered unreliable because the underlying infrastructure is assumed to be unreliable. Therefore, IP allows a data transmission to adapt to the actual condition of the underlying network. There are two versions of IP in use: IPv4 and IPv6, as we have already seen. IP and TCP normally work together, and are known as TCP/IP |
| GRE | GRE (Genetic Routing Encapsulation) is a tunnel protocol that is used to encapsulate other protocols. The way it works is that a normal data packet is encapsulated inside an IP packet. Routers along the route do not look at the internal packet, only the outside. The final destination looks inside the internal packet. GRE is not secure. |
| IPSec | IPSec (Internet Protocol Security) is a protocol that allows two devices to create a tunnel between them across a normal internet connection. IPSec encapsulated the existing data packet into a larger packet. The interior packet is also encrypted so that routers along the way can’t see inside. |
Connection-oriented protocols require a connection to be established. That is, two devices agree to communicate with each other.
- A connection-oriented protocol is like two people approaching each other at a park and agreeing to have a conversation:
- Person One: “Hey can I talk to you?”
- Person Two: “Sure”
- Person One: “Okay, blah, blah, blah”
- Person Two: “I acknowledge what you said”
- The communication is two ways. The two devices must work to establish the connection, acknowledge the connection and agree on how they will communicate throughout the connection
- The two devices will also mutually agree to end the connection once the communication is complete (or a device can unilaterally end the connection if it doesn’t hear from the other party after some time).
- The communication involves two parties and only two parties
- The recipient acknowledges receipt of each communication
- TCP is a connection-oriented protocol, and uses a three-way handshake to establish the connection)
- The first message is called the SYN (hey can I talk to you?)
- The second message is called the SYN-ACK (yes you can!)
- The third message is called the ACK (I understood that)
- The first message is called the SYN (hey can I talk to you?)
- A connectionless protocol is like one person climbing to the top of a hill and yelling at somebody at the bottom of a hill. Nobody agreed to talk to him. He might talk to only one person, or he might talk to many people. The other person might yell back. The other person might not even be there, in which case he will be talking to himself and not know it.
- The communication is one way
- The communication may be directed at one recipient or many.
- Nobody knows if the intended recipient received the message, because the recipient has no way of acknowledging receipt
- If we’re broadcasting a live video stream, we might use a connectionless protocol because it allows anybody to tune in
- The communication is one way
