4.2 Compare and contrast common types of attacks
- Technology-Based
- Denial-of-Service (DoS) / Distributed Denial-of-Service (DDoS)
- Botnet / Command and Control
- On-Path Attack (Man-in-the-Middle)
- DNS Poisoning
- VLAN Hopping
- ARP Spoofing
- Rogue DHCP
- Rogue Access Point (AP)
- Evil Twin
- Ransomware
- Password Attacks
- Brute Force
- Dictionary
- MAC Spoofing
- IP Spoofing
- Deauthentication
- Malware
- Denial-of-Service (DoS) / Distributed Denial-of-Service (DDoS)
- Human and Environmental
- Social Engineering
- Phishing
- Tailgaiting
- Piggybacking
- Shoulder Surfing
- Social Engineering
Now that we have an idea of risk management, let’s look at some ways that our network can be attacked.
DoS is Denial of Service. There are millions of servers operating on the internet (which host websites). If a hacker wants to bring down a web server, the hacker would flood that server with massive amounts of traffic. The web server would then be unable to respond to legitimate traffic, and ordinary users would be unable to visit the website. This is known as denial of service. Services other than websites exist on the internet (credit card processing, databases, etc.), and all are vulnerable to DoS.
There are many types of DoS attacks
- SYN flooding. Remember that when a user wants to connect to a web server, a three-way handshake (SYN, SYN/ACK, ACK) process occurs between the two computers.
- The user sends a SYN message to the server; the server responds with a SYN/ACK message to the user, and the user responds with an ACK message to the server
- In SYN flooding, the hacker imitates a legitimate user and sends more SYN requests than the web server can handle. The web server opens a connection for each SYN request and responds with the SYN/ACK response, but the hacker does not complete the third part of the connection by sending the SYN.
- The server keeps a connection open waiting for an ACK message that never arrives. The server can only keep a limited number of connections open. If all of them are waiting for ACK messages that will never arrive, then the server won’t be able to establish connections with legitimate users
- The user sends a SYN message to the server; the server responds with a SYN/ACK message to the user, and the user responds with an ACK message to the server
- Fragmenting. When data travels over the internet, the sending computer breaks it down into pieces known as packets. The packets may take different routes to reach their destination. The receiving computer puts the packets back together. The data in each packet should not overlap.
- In a fragmenting attack, the hacker send data to the server, but puts overlapping data into each packet
- The server attempts to put the data back together but can’t. If the operating system isn’t equipped to recognize this attack and discard the bad packets, then the server will crash.
- In a fragmenting attack, the hacker send data to the server, but puts overlapping data into each packet
How to prevent Denial of Service
- Most DoS attacks are preventable now. Why?
- A hacker will not have enough bandwidth to bring down a large web service. Major websites such as Google, Facebook, eBay, etc. use distributed server farms consisting of millions of servers, with redundant pathways to the internet. A hacker will not have enough capacity to overload their systems.
- Most enterprise systems contain firewalls that can easily detect and block DoS attacks. If a substantial amount of illegitimate traffic appears to be originating from a single source, it can simply be turned off.
- For a small monthly fee, services such as CloudFlare offer large-scale cloud-based firewalls to protect smaller websites from DoS attacks (which they normally could not afford).
- A company should never be a victim to the same attack twice. After the first attack, they must investigate and rewrite their systems so that it never happens again. The most common types of attacks are well documented, and systems are available to prevent them.
Distributed Denial of Service was invented after DoS stopped working (due to improvements in internet infrastructure).
With DDoS, a hacker infects thousands (or hundreds of thousands) of computers (or other IP devices such as cameras) and uses all of them to send traffic to a web server that he wants to crash. These computers are known as bots, and together they are known as a botnet. Since the traffic appears legitimate (and is in fact originating from hundreds of thousands of different sources, in different geographic locations, different internet service providers, and different computer types), it is difficult to filter or prevent.
The botnet operator will continue to acquire additional bots, to grow his botnet. The operator will lease his network of bots to a person or organization that wants to bring down a website (for revenge, competition, or other reasons).
Examples of bots
- Mirai. Most web-accessible routers and IP cameras come preconfigured with default usernames and passwords. Most home users of routers and IP cameras neglect to change the default usernames/passwords (in some cases, it is impossible to change the default username/password).
Mirai scanned IP addresses at random and located web-accessible routers and IP cameras. It then attempted to log in using default usernames/passwords. Once successful, it infected the devices. Once infected, the devices are added to the botnet and used to launch attacks.
How to prevent
- Services such as CloudFlare use large scale cloud-based firewalls to mitigate DDoS attacks. They set up a server farm with a large amount of bandwidth that can be “donated” to a website facing a DDoS attack. CloudFlare’s bandwidth can accept some DDoS attacks.
- Users should use antivirus and firewall programs to prevent their computers from becoming infected and turned into bots.
- Users should ensure that they change the default username and password on their IoT devices.
- Manufacturers of IP cameras and wireless routers should put in the effort to make their devices more secure (so that they do not become infected and used in DDoS attacks).
In a Man-in-the-Middle attack, a hacker inserts himself between the sender and recipient of an electronic communication. Keep in mind that more than 60% of internet traffic is machine generated (one computer talking to another with no human interaction).
Consider that Alice and Bob are two hypothetical internet users having an encrypted conversation. They could be two humans, or it could be that Alice is an online banking user and Bob is the bank. Consider that the hacker, Eve, wants to spy on them.
Alice and Bob’s messages pass through a central server. Depending on Alice and Bob’s geographical locations, the messages may pass through many servers, routers, switches, fiber optic cables, and copper lines. The internet is fragmented, and different parts are owned by different companies. If Alice is in New York and Bob is in Los Angeles, the traffic must pass through many states, and many internet service providers.
- If the traffic between Alice and Bob is unencrypted, and Eve can obtain access to one of the servers, routers, switches, or physical connections, then Eve can spy on the conversation.
- If the traffic is unencrypted, but Eve does not have access to one of the servers in the connection, Eve could trick Alice into sending messages addressed to Bob to her instead (by corrupting/modifying Alice’s address book). Eve would do the same to Bob.
In Alice’s address book, Eve replaces Bob’s address with her own.
In Bob’s address book, Eve replaces Alice’s address with her own. Alice sends messages to Eve thinking she is sending them to Bob, and Bob sends messages to Eve thinking he is sending them to Alice.
Now Eve can read Alice’s messages and forward them to Bob. Eve can also read Bob’s messages and forward them to Alice. Neither Alice nor Bob is aware that Eve is reading their communications. - If the communication is encrypted and uses public key cryptography (such as Apple iMessage or WhatsApp), a man-in-the-middle attack is more difficult.
- Consider how public key cryptography works
- Alice and Bob each creates a private key which they keep secret. A private key can only decrypt a message
- Alice and Bob use the private key to generate a public key, which they distribute to potential senders. A public key can only encrypt messages.
- If the keys are long enough, they cannot be reversed. As long as the systems and algorithms are secure, it would be practically impossible to decrypt a message without the private key.
- If Alice wants to send Bob a message, she finds his public key. She encrypts the message using his public key, and then send him the encrypted message. Bob receives the encrypted message and uses the private key to decrypt it.
- Apple iMessage and WhatsApp automatically generate the keys for each user. If Bob is using an iPhone, his iPhone will generate a private key, which it will store on the phone. It will also generate a public key, which is stored in Apple’s central directory.
- If Alice wants to send you Bob a message via iMessage, her iPhone checks the Apple directory for his iPhone’s public key, which it uses to encrypt the message.
- Alice and Bob each creates a private key which they keep secret. A private key can only decrypt a message
- Consider how public key cryptography works
- What if Eve wants to intercept an iMessage or WhatsApp communication between Alice and Bob?
- Eve generates her own public and private keys
- She hacks into the central directory and changes Bob’s public key to her own. She records Bob’s original public key.
- Alice decides to send a message to Bob. She checks the directory for Bob’s public key, and receives what she thinks is Bob’s public key (but is in fact Eve’s public key)
- Alice sends the message to Eve (thinking she is sending it to Bob)
- Eve decrypts the message, reads it, and then encrypts it with Bob’s original public key
- Eve sends the message to Bob
- Bob receives the message, thinking it came from Alice and decrypts it with his own private key
- Eve repeats the same process with Alice’s public key so that she can intercept messages that Bob is sending to Alice
- Eve generates her own public and private keys
How to prevent
- The best way to prevent a man-in-the-middle attack is to encrypt all communications with a reliable encryption algorithm (one that uses a long enough key length and is generated through open-source methods)
- Second, ensure the integrity of the public key. Do not trust applications with “key directories” such as Apple iMessage or WhatsApp, especially for sensitive communications.
Apple controls all the public keys in iMessage and a rogue operator could inject their own public keys, creating the man-in-the-middle attack illustrated above. The best way to ensure the integrity of the public key is to personally distribute it to the person that you want to communicate with.
What is DNS? Recall that every computer on the internet has a unique IP address. That means, every website’s server has a unique IP address. Humans are not good at remembering IP addresses. If you had to remember and type in the IP address for every website you visited, the internet would not be very useful. Instead, you type in a domain name, such as google.com.
The DNS (Domain Name System) knows what every domain name is, and what its corresponding IP address is. When you type in a Domain Name, your computer queries the DNS to find the correct IP address for that website’s server.
Who operates DNS
- There are many online public DNS servers such as Google DNS (8.8.8.8 and 8.8.4.4). These provide records for publicly-available websites.
- Many ISPs operate DNS servers for their own customers. These provide records for publicly-available websites and are only accessible to their own customers. For example, Comcast might operate a DNS for their own customers. A customer can choose to bypass Comcast’s DNS and use Google’s DNS.
- Many companies operate their own DNS servers for their own offices. These provide DNS for internal systems and internal websites and may also provide DNS for publicly-available websites. A public DNS would not be able to provide a DNS record for an internal device.
- Each Windows machine operates its own DNS to keep track of the most recently visited websites.
An authoritative DNS server (or nameserver) holds the original records for the hostname in question. Different DNS servers can be authoritative for different websites. A recursive (non-authoritative) DNS server is one that requests DNS data from the authoritative DNS server.
- For example, AWS Route 53 DNS Servers are authoritative for amazon.com because they hold amazon.com’s original DNS records
- If a user queries the AWS server, he will receive an authoritative answer about the location of the amazon.com servers
- After querying the AWS DNS server, DNS servers at the user’s ISP and office cache the DNS data. Now, DNS servers closer to the user know the IP address of amazon.com.
- The user (or other users) can go back to these servers to perform DNS lookups, but the answer will be non-authoritative. They don’t have to query the authoritative DNS server, which is far away.
In DNS Poisoning, a hacker corrupts the DNS records. The hack can take place at the top-level DNS servers, at the ISP level, at the office level, or at the computer level. The corrupted DNS can force a user to visit a fake server.
- For example, Bank of America’s web server is located at IP address 11.11.11.11
- A hacker sets up a server at 9.9.9.9 and then corrupts the local DNS server to point users to Bank of America’s website at 9.9.9.9. The users’ computers visit the website at 9.9.9.9 thinking they are accessing a legitimate Bank of America server.
How to prevent
- Use an authoritative DNS server. An authoritative DNS server is one that provides original DNS data. An authoritative DNS server can be hacked, but it is less likely.
- Use Domain Name System Security Extensions (DNSSEC). DNSSEC uses digital signatures to authenticate DNS information.
Each domain name server digitally signs the response it provides. The recipient can validate the signature to ensure that it received a legitimate record.
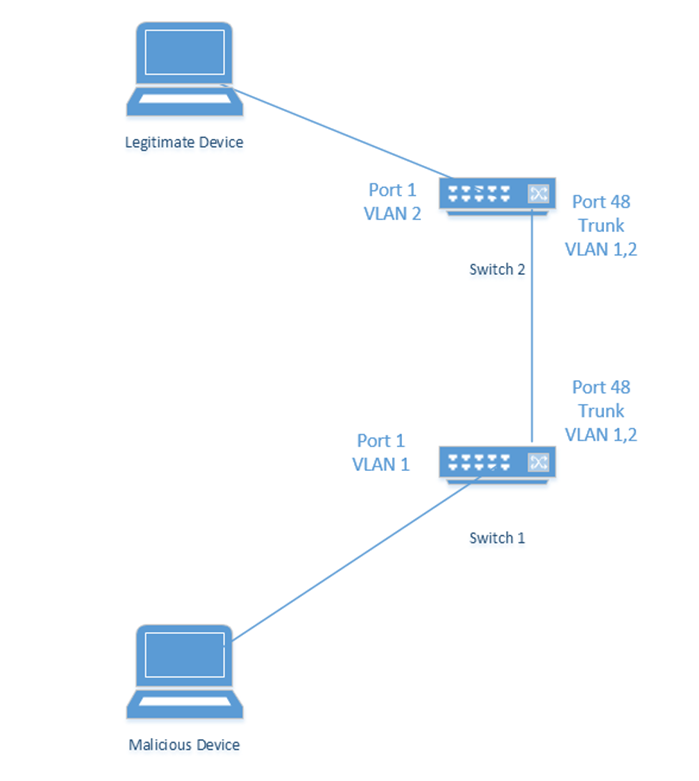
VLAN Hopping is a trick where a device can gain access to traffic on VLANs that it is not entitled to. Recall that a VLAN can be used to segment network traffic. Remember that a switch can have “access” ports, which transmit traffic on only one VLAN, and “trunk” ports, which transmit traffic on multiple VLANs.
When we connect a device (such as a laptop for example) to an access port, the device can access the network on the VLAN that is specified on that port.
We would normally connect two switches together on switches configured as trunk ports. If we didn’t explicitly configure the ports as trunks, when we connect two switches together, those switches may attempt to negotiate a “trunk” and agree to exchange traffic on multiple VLANs.
A malicious device connected to a switch can pretend that it is also a switch, with a trunk port. The other switch would then establish a trunk and exchange traffic on multiple VLANs. We can prevent this by configuring our switch ports explicitly – that means telling each port to act as either an access port or as a trunk port. A device connected to an access port will not be able to move to another VLAN.
If we don’t explicitly set a VLAN, then the default VLAN on an access port is VLAN 1. The default VLAN is also known as the native VLAN. The switch will ignore any frames tagged with the native VLAN of the port.
A malicious device can tag a frame with two VLANs – the native VLAN, and the VLAN of a device that it wants to exploit. This is known as a double-tagged frame. The switch will ignore the native VLAN tag and forward the frame with the second tag. If the trunk port has a native VLAN, then the trunk port will not attempt to retag the frame. If the device to be exploited is connected to a second switch, then that second switch will accept that frame on the VLAN.
For example,
- A legitimate device is connected to Port 1 of Switch 2, VLAN 2
- A malicious device is connected to Port 1 of Switch 1, VLAN 1 (the native VLAN)
- The two switches have a trunk that passes traffic from VLAN 1 and VLAN 2
- The malicious device should not be able to communicate with the legitimate device because they are on different VLANs
- If the malicious device double-tags a frame with VLAN 1 and VLAN 2, and addresses it to the legitimate device
- Switch 1 will receive the frame and ignore the tag for VLAN 1
- It will send the frame to Switch 2 over the trunk port
- Switch 2 will see that the frame is tagged for VLAN 2 and addressed to the legitimate device
- Switch 2 will forward the frame to the legitimate device
- Switch 1 will receive the frame and ignore the tag for VLAN 1
How can we stop this from happening?
- We should make sure not to use VLAN 1 for anything.
- We should explicitly configure each access and trunk port VLAN
- We should ensure that the native VLAN on a trunk port is changed to one that is not used.
ARP is Address Resolution Protocol. Remember that every network device has a unique MAC address, set from the factory. A MAC address is kind of like a serial number. When a device connects to a network, it announces its MAC address.
Every device is assigned (or should be assigned) a unique IP address. On a LAN (Local Area Network), devices communicate by addressing data to the each other’s MAC addresses.
If the sender knows the recipient device’s IP address, but not it’s MAC address, it uses ARP to discover the MAC address. It does so by flooding the network with a request for the MAC address. Since the device doesn’t know who it is looking for, every device on the network receives the request. It sends the electronic equivalent of a “hey if this is your IP address, reply with your MAC”. The device in question replies with its MAC address.
The opposite is also possible. A device can flood the network with a request for an IP address when the MAC address is known. This is known as reverse ARP or RARP.
Each network device stores common MAC addresses and their corresponding IP addresses in a table known as the ARP table, so that it doesn’t have to look them up each time it needs to send data (too many ARP lookups can overload the network).
There is no authentication mechanism for the ARP table. Each device simply adds/updates the ARP table when data is received. A device will update the ARP table with new data even if it did not create an ARP request. There is no way to check if a device has lied about its MAC address.
ARP Poisoning is when a hacker sends wrong data to corrupt the ARP table.
- Let’s say our office has a printer with an IP address of 10.10.1.1 and a MAC address of AB:CD:EF:12:34:56
- Bob wants to print some sensitive documents. His computer knows that the printer’s IP address is 10.10.1.1 but doesn’t know its MAC address. It sends out an ARP request to 10.10.1.1, and the printer responds with AB:CD:EF:12:34:56
- Bob’s computer stores this data in its ARP table
- Bob’s computer sends documents to be printed to AB:CD:EF:12:34:56
- A hacker comes along and plugs a laptop into an open ethernet port in Bob’s office. The hacker’s laptop has an IP address of 10.10.1.2 and a MAC address of AA:BB:CC:11:22:33
- The hacker sends out an ARP message saying that 10.10.1.1 belongs to AA:BB:CC:11:22:33, the hacker’s computer
- Bob’s computer picks up this unsolicited ARP message and stores it in the ARP table
- Bob’s computer sends all printed documents to the hacker’s computer instead of the printer
- The hacker can forward Bob’s documents to the printer, so that they print correctly, and Bob doesn’t suspect that his documents have been stolen
How to prevent
- Obviously, the hacker should never have been able to plug his laptop into an open ethernet port in Bob’s office.
- Somebody should have noticed that there was an intruder and called the police
- An open ethernet port should never be patched into a switch
- The hacker’s laptop should never have been permitted to access the network, even if the port was open
- But many offices do not have adequate security
- Somebody should have noticed that there was an intruder and called the police
- Use ARP spoofing detection software. The software can perform cross-checking of ARP entries against a DHCP server or switch, which has accurate information.
- Critical system components should have static ARP entries that cannot be changed. This could require a substantial amount of maintenance for hosts use DHCP.
A hacker who found an open ethernet port could connect a rogue DHCP server (any small router will have a DHCP server built in) and attempt to take the other network devices offline. Each time a device attempts to obtain an IP address via DHCP, the rogue DHCP server responds faster than the legitimate server.
Eventually, many devices receive IP addresses issued by the rogue DHCP server and are unable to access the internet or other devices on the network.
The hacker can take this one step further and specify his own default gateway as part of the DHCP configuration. Now devices receiving DHCP configuration from the rogue server will forward their external traffic to a rogue default gateway.
We can prevent a rogue DHCP server from operating by enforcing MAC address filtering on the network. We can also use DHCP snooping.
There are many types of wireless attacks.
- Evil Twin. A wireless client will connect to the access point that has the highest signal (typically the one that is nearest to the client). In an Evil Twin attack, the hacker deploys a wireless access point with the same SSIDs as the legitimate access points, but with a higher signal strength. Clients that are preconfigured to connect to the SSIDs will connect to the evil twin.
The evil twin attack can be prevented by authenticating all wireless connections through certificates. The client should be configured to verify the identity of the network that it is connecting to. A rogue access point will not be able to prove its identity.
- Rogue AP. A Rogue AP is an evil twin that forwards traffic to the main network. The Rogue AP allows a hacker to act as a man-in-the-middle and intercept all traffic.
Preventing Rogue APS can be done by- Using access points that detect Rogue APs (for example, Cisco Aironet APs have optional Rogue AP detection modules)
- Using MAC address filtering on the network to prevent unauthorized devices from connecting
- Using access points that detect Rogue APs (for example, Cisco Aironet APs have optional Rogue AP detection modules)
- Jamming. Wireless Access Points operate on a specific band of the electromagnetic frequency spectrum (2.4 GHz and 5 GHz). A hacker can flood the air with useless signals in the same frequency. If these signals are more powerful than those put out by the access point, they will prevent legitimate users from connecting. Signal jamming has applications in other types of networks (cell phone jamming, radar jamming).
- Disassociation. In a disassociation attack, a hacker forces a client to disassociate from an access point. A hacker can force a client to disassociate from an access point by sending a “disassociation” message to the client.
- The disassociation message is a standard message that an access point could sent to a client to disconnect it
- It contains the MAC address of the client and the SSID of the access point
- If a hacker intercepts communication between the client and the access point, he could learn the MAC address of the client, and then create a fake disassociation message
- The hacker must send these messages to the client constantly, or it will try to reconnect. This creates a cycle where the client is constantly stuck between connecting to and disconnecting from the wireless network.
- The disassociation message is a standard message that an access point could sent to a client to disconnect it
Crypto-malware and ransomware are closely related. Crypto-malware is a type of virus or malicious program that encrypts data on a computer.
The malware can be introduced through e-mail or downloaded files. The malware usually encrypts user documents, videos, photos, and music. It does not usually encrypt system files.
The distribution of crypto-malware is usually automated, although people or organizations can be specifically targeted. It should be noted that after the crypto-malware has infected the computer, then the author is able to view the contents of the computer. At that point, he can make an assessment as to how high of a ransom to charge. For example, if an ordinary person was targeted, the ransom might be low, but if a hospital was targeted, then the ransom might be high.
After infection, the computer operates as normal, but the user is provided with a message that their files have been encrypted. The malware usually instructs the user to pay a ransom to unlock the files. The ransom must typically be paid in bitcoin or another cryptocurrency that can’t be traced.
There are two types of crypto-malware
- Crypto-malware that pretends to encrypt the files. They change the file extension to something random, but do not encrypt the file. A non-sophisticated user will assume that the files are encrypted because an error message will be encountered when the file is opened. If the extension is changed back to the original, the files revert to normal. These forms of crypto-malware are extremely rare.
- Crypto-malware that encrypts the files. After the files are encrypted, the decryption key is sent to a central server maintained by the hacker. The user receives the decryption key after paying the ransom.
Files encrypted by some forms of crypto-malware cannot be decrypted, either because the crypto-malware is misconfigured, or because the hacker’s intention is to permanently encrypt the files.
Ransomware is an extension of crypto-malware, in that it instructs the user to pay a ransom in exchange for unlocking the files.
Typically, the user is instructed to visit a TOR website, where they are provided further instructions. TOR websites are generally able to hide the location of their servers, although law enforcement agencies have developed methods to identify them. The user is instructed to pay the ransom with cryptocurrency (untraceable currency) such as bitcoin.
In most cases, the hackers provide the victim with the tool to decrypt their files upon receipt of payment. In some cases, the hackers do not.
The ransom amounts have ranged from the equivalent of $500 to $20,000 depending on the person or organization that was affected. Many organizations pay the ransom and don’t publicly admit that they have been hacked.
How to prevent ransomware
- Proper user education to teach users how to identify potential ransomware delivered via e-mail, and to not open unusual attachments.
- Block e-mail attachments that contain macro-enabled Microsoft Word and Excel documents.
- Regularly install Windows operating system security updates
How to defeat ransomware once infected
- Attempt to restore data from backup or from the Volume Shadow Copy. This only works if the organization has backed up their data, and only the data that was backed up can be restored. Newer versions of ransomware delete the Volume Shadow Copy.
- Attempt to decrypt the ransomware. Police forces in the EU have been able to provide victims with assistance in decrypting some forms of ransomware. Some versions of ransomware use weak encryption that can be broken through brute force or other techniques.
- Pay the ransom. In earlier cases, it was almost certain that the hackers would automatically (or manually) provide the decryption key upon payment of the ransom. In more recent cases, this is not guaranteed because there are many copycat ransomware viruses created by people with very little knowledge or infrastructure. Ransomware developers have franchised their operation to “script kiddies” who are simply distributing the ransomware and collecting payments. There are also versions of ransomware that have been put out by nation-states to cause political disruption; this type of malware only destroys data but is disguised as ransomware.
Notable infections
- In 2019, Jackson County, Georgia paid $400,000 to remove ransomware from their computers.
- University of Calgary paid $20,000 to decrypt computers infected by ransomware in 2017. The FBI later charged two people in Iran with spreading the virus, which infected computers at health care providers and other organizations.
Notable ransomware
- CryptoLocker was transmitted over e-mail as a ZIP file. Inside the e-mail was an executable disguised as a PDF. The decryption key was sent to a remote server. A victim could pay a ransom and receive a decryption key automatically. The creators of CryptoLocker made an estimated $27 million. In 2014, security firm FireEye was able to obtain the database of decryption keys, allowing victims to decrypt their files for free.
- WannaCry took advantage of a zero-day exploit in the Windows Server Message Block. WannaCry infected computers that had not patched the Windows Server Message Block vulnerability. The average ransom amount was $600. Over 200,000 computers were infected, with losses estimated at over $4 billion.
- Unlike other forms of ransomware, Petya encrypted the master boot record of a Windows computer. This caused the entire computer hard drive to be encrypted. Another version, known as NotPetya was targeted towards Ukrainian government entities and critical infrastructure. NotPetya quickly spread to other computers worldwide and could not be decrypted. It is believed that NotPetya was created by the Russian government.
Some ways that a hacker can attempt to decrypt a password
- Rainbow Tables. It is bad security practice to store passwords in plain text. Passwords are typically hashed, and the hash is stored (the hash is not reversible). A hash is a one-way mathematical function. Thus, when the password is created, the hash is generated and stored. Each time the user logs in, the password entered is hashed; this hash is compared against the stored hash to determine whether it is correct.
If a database of hashed passwords is leaked, the hackers will only see the hashes, which cannot be reversed back to the original passwords. The hash can’t be used to log in.
But a hacker could generate a dictionary of passwords (common and uncommon) and calculate the corresponding hash for each one. This reference is known as a rainbow table. The hacker could then steal a database of password hashes and look up the corresponding password for each one.
Rainbow tables are readily available on the internet for passwords up to eight characters (every possible combination!) and rainbow tables of even longer passwords can be computed.
To prevent the use of rainbow table attacks, modern password hash functions incorporate a ‘salt’. The salt is a random set of characters appended to the end of each password before the hash is calculated. The hash and the salt are stored in plain text. If the hash database is compromised, the hacker would have to regenerate each rainbow table incorporating the salt into every password to make any sense of it. This would be practically impossible. - Dictionary. A Dictionary attack uses a list of predetermined passwords and brute force to guess the password. The dictionary could consist of common words in the English language, especially common passwords such as “password”, “12345678”, and “abcd”.
A hacker could create a custom dictionary based on the user account that he is trying to hack into. For example, the dictionary could be customized to include the names of the user’s children, pets, vehicles, etc..
Many organizations force users to choose complex passwords. Password complexity could include- Not reusing the same password
- Including upper case letters, lower case letters, numbers, and special characters
- Ensuring that the password meets a minimum length
- Not using a person’s name, address, or username in the password
- Not reusing the same password
Yet, it is still possible to create a custom dictionary based on the password complexity requirements. For example, if the user’s password was ‘donkey’, then a complicated password might be ‘D0nkey!’. Users tend to substitute @ for a, 0 for o, 1 for l, and so forth in a predictable manner.
A dictionary attack can be prevented by limiting the amount of password attempts a user has before his account is locked out. Of course, the dictionary attack could occur offline, or the hacker may have a way to bypass the incorrect password attempt count.
- Brute Force. A brute force attack is like a dictionary attack, except that the system attempts every password combination possible (based on the character set), starting from the letter a and working its way up until the password is guessed. For example, the system will guess the password ‘sdfsfgdgsdfsdfd’, and then the next password would be ‘sdfsfgdgsdfsdfe’.
The length of time for a brute force attack to be successful depends on the computing power available (how many passwords can be attempted every second) and the length of the password (how many passwords need to be attempted).
An online brute force attack is when the brute force occurs against a live computer. For example, consider Active Directory, a Microsoft system that stores user accounts on a central server. When a user attempts to log in to an Active Directory-based computer, the computer validates the login credentials with the server. On a successful login, the computer caches the correct credentials on the local computer. If the computer is later offline (or off the local network), the user can still log in (the computer validates the login with the cached credentials).- In an online attack, the hacker would brute force the computer’s login while it is connected to the Active Directory server. This attack would likely be unsuccessful because the server would notice the incorrect logins and disable the account.
- In an offline attack, the hacker would brute force the computer’s login while it is not connected to the Active Directory server. This attack may or may not be successful depending on the length and complexity of the password.
- In an online attack, the hacker would brute force the computer’s login while it is connected to the Active Directory server. This attack would likely be unsuccessful because the server would notice the incorrect logins and disable the account.
How to prevent
- Offline attacks can’t be prevented. Where possible, secure equipment so that it is not stolen. Stolen equipment is more susceptible to offline attacks.
- Enforce stronger password requirements (including special characters, numbers, upper/lower case letters).
- Enforce a timer that delays the entry of passwords. This can be accomplished at the software or hardware level, by hashing the password multiple times.
- Offline data can be encrypted with a strong algorithm that takes several seconds to validate the password. This would be a minor inconvenience to a user entering an incorrect password but would substantially slow down a brute force attack.
- If the computer is secured with a password but the data on the computer is not encrypted, the hacker might have other ways to compromise the device. Then the password is ineffective regardless of its length or complexity.
- Enforce stronger password requirements (including special characters, numbers, upper/lower case letters).
Recall that each network device is manufactured with a unique, unmodifiable (in theory) MAC address. On a LAN, one security measure to prevent rogue devices is to only allow traffic between trusted MAC addresses. If an intruder attempts to connect a new device to the network, it will not be permitted to communicate because its MAC address is not on a list of authorized devices.
If a hacker learns the MAC address of a legitimate network device, he can change his device’s MAC address and gain access to the network (and to the traffic originally directed to the legitimate device).
How to prevent
- Require additional user authentication before allowing a device to access the network
- Use port security on switches. A switch can remember which MAC address sent traffic on which port. If the switch detects the same MAC address on a different port, it can either shut down the port or alert an administrator of the discrepancy.
Recall that each network device is assigned a unique IP address. Two network devices can communicate over a LAN or public network if they know each other’s IP addresses. A hacker can intercept their communication by changing his machine’s IP address to match that of one of the devices. This method takes special skill and control/modification of network routers, because
- Most network devices/computers will detect the IP address conflict.
- The device whose IP address is spoofed will not receive any traffic because it is being intercepted by the hacker’s computer. The hacker’s computer would pretend to be the legitimate computer and carry on the communication.
- To remain undetected, the hacker will have to intercept the IP traffic through the router and then forward it to the legitimate recipient.
A broadcast IP address is a special type of IP address that exists in every network. The broadcast address allows a device to send a single message to all the IP addresses on that network. One type of broadcast message is known as an “echo”. Devices receiving the “echo” message reply to the sending device.
In a Smurf Attack, the hacker forges the “from” portion of the echo message so that it appears to have come from another system (the system that he wants to attack). The device whose address appears in the “from” portion will receive all the replies. Depending on the size of the network, and the number of echo messages sent, that device could receive hundreds or thousands of replies. A Smurf Attack is like an internal DDoS attack.
How to prevent
- Encrypt all traffic. An IP spoofing attempt will not allow a hacker to read encrypted traffic.
- Set firewalls to drop traffic that originates from outside the network but appears to come from inside the network (could indicate that the address has been spoofed).
Malware is a general term given to programs that are illegitimate. They include viruses, trojans, and worms.
A virus is an unauthorized program that causes undesired activity. A virus is not a standalone program, but instead it latches on to another legitimate program. When the legitimate program runs, so does the virus.
Viruses typically infect executable programs such as programs with extensions of .exe. Viruses can also infect documents, such as Microsoft Word documents or Microsoft Excel spreadsheets. These are known as macro viruses. Current versions of Microsoft Office disable macros by default (a user can open a Microsoft Office document file without allowing the macro to execute).
Viruses can enter automatically through vulnerabilities. A user could inadvertently introduce a virus by clicking on attachments or downloading files from the internet.
The damage that a virus does is called the payload. Viruses can cause a wide range of effects from being simply a nuisance to deleting files. Viruses that infect industrial control systems can cause millions of dollars in damage. Viruses that infect medical equipment can put lives at risk.
A virus can be detected and prevented using an antivirus program. An antivirus program has two methods of detecting viruses
- Definitions: A definition is a specific “fingerprint” of the virus. An antivirus program may contain hundreds of thousands of virus definitions. It scans each new file introduced into the computer against the definitions. If the attributes of a file match a definition, then the antivirus program knows that it has located a virus (and knows which virus it has located).
To develop the antivirus definitions, the antivirus software manufacturer must first obtain copies of the virus and create the definition. That means that some computers have already been infected with the virus by the time the definition has been created. Thus, definitions do not provide complete protection against viruses.
A polymorphic virus is one that attempts to change its code. Each time the virus runs, the code changes slightly, but the damage that it causes remains the same. A polymorphic virus attempts to hide from antivirus definitions. - Heuristics. A heuristic is a type of artificial intelligence. It allows the antivirus program to determine whether a specific program is legitimate or not, based on its behavior. For example, a program that attempts to modify critical system files is likely not legitimate.
The latest generation antivirus programs share data with the cloud. For example, Norton Antivirus automatically collects data regarding suspicious applications from users. This data is sent to a response center for further analysis. Norton Antivirus then updates all user programs with the results. By sharing data with the cloud, antivirus programs are able to detect viruses faster.
The most famous computer viruses have been
- ILOVEYOU. Released in 2000, ILOVEYOU was transmitted via e-mail with a subject line of “I love you”. It overwrote system files and personal files, before spreading through e-mail. It caused $15 billion in damage.
- MyDoom. Similar, to ILOVEYOU, MyDoom spread via e-mail in 2004. It is estimated that 25% of all e-mails sent in 2004 were infected with MyDoom. It caused $38 billion in damage.
- Stuxnet. Stuxnet is a special kind of virus because it infected the firmware of a USB drive. The firmware of a USB drive is not typically accessible to the computer or to an antivirus program – it’s considered “read only” memory and allows the USB drive to read/write data from/to the computer.
The Stuxnet virus contained a second virus inside of it. When the USB drive was inserted into a PLC (an industrial control system), the second virus infected the PLC. Stuxnet only infected Siemens S7 PLCs.
Stuxnet was used to infect industrial control systems that were “air gapped” (not connected to the internet or to any network).
Stuxnet was unusual because- It took advantage of multiple zero-day exploits (security holes that are unknown to the software manufacturers). A zero-day exploit is considered valuable to a virus manufacturer/hacker, and to use several in the same virus is highly unusual. Zero-day exploits are quickly patched by manufacturers once discovered and can’t be reused. A zero-day exploit could be worth up to a million dollars. To use several million dollars worth of zero-day exploits in a virus that brings the creator no financial reward is highly unusual.
- It limited its infection to only specific types of computers and PLCs. Most virus manufacturers do not want to limit the damage that they cause.
- It is estimated that Stuxnet took between three man-years and fifteen man-years to prepare. Development of Stuxnet required advanced knowledge of the Windows operating system, USB firmware, and Siemens PLCs.
- It took advantage of multiple zero-day exploits (security holes that are unknown to the software manufacturers). A zero-day exploit is considered valuable to a virus manufacturer/hacker, and to use several in the same virus is highly unusual. Zero-day exploits are quickly patched by manufacturers once discovered and can’t be reused. A zero-day exploit could be worth up to a million dollars. To use several million dollars worth of zero-day exploits in a virus that brings the creator no financial reward is highly unusual.
The difference between a worm and a virus is that the worm replicates by itself, whereas the virus must attach itself to a legitimate file. The virus only runs when the legitimate file runs.
Worms can generally spread over a network from computer to computer, by themselves. They take advantage of security holes.
Examples of worms
- SQL Slammer took advantage of a buffer overflow bug in Microsoft SQL Server. The worm would randomly generate IP addresses and then send itself to those IP addresses. If the IP addresses belonged to computers that were running an unpatched version of SQL Server, then the worm would be successful in infecting them. The worm caused many internet routers to crash, and reboot. Each time the routers rebooted, they would resend routing updates to each other, which would cause internet traffic congestion. SQL Slammer was exceptional in that it fit inside a single data packet.
A trojan is a legitimate program that hides an illegitimate program. A user must install the trojan and/or give it permission before it can take effect. Trojans are named after the Trojan horse.
Trojans can hide in many programs including toolbars, screensavers, games, and other applications.
Examples of Trojans
- FinFisher (FinSpy), which is developed by Lench IT Solutions plc. This trojan is used to infect Windows computers and all brands of phones. It travels through e-mail, links, and security flaws in popular programs. Many antivirus programs are unable to detect it.
FinFisher is sold to law enforcement agencies and dictatorships, some of which are accused of numerous human rights violations.
A rootkit provides unauthorized administrative level access to a computer by changing its operating system and attempting to bypass its security functions.
There are five types of rootkits
- Firmware. A firmware rootkit hides inside the device firmware (such as the BIOS, video card controller, router, network card, or hard drive controller). The device firmware is not typically scanned by (and is out of reach of) antivirus programs. While manufacturers such as HP have introduced BIOS integrity features that check for changes to the BIOS firmware, rootkits can infect other components such as the graphics card or hard drive.
- Virtual. A virtual rootkit is also known as a hypervisor rootkit. It operates between the processor and the operating system. It intercepts calls made by the operating system, like a “man-in-the-middle” attack. The result is that the processor believes that it is talking to the operating system and the operating system believes that it is taking to the processor, but, both are talking to the rootkit. The rootkit sends everything it learns to a central server.
- Kernel. A kernel rootkit runs on a computer with the highest privileges (the same privileges as the operating system) by replacing parts of the operating system core and device drivers. A kernel rootkit can’t be detected by an antivirus program because the rootkit is acting like part of the legitimate operating system.
- Library. A library level rootkit replaces legitimate operating system DLLs with fake ones. A library is a set of code/functions that an application can reference (a software developer will include different DLLs with their application so that they don’t have to rewrite thousands of lines of code for common functions). When an application references code in an infected DLL, the rootkit will also run.
- Application Level. An application level rootkit replaces application files with fake versions. The application may need to run at an elevated level in order to cause damage.
Examples of rootkits
- LoJack. LoJack is a legitimate rootkit that comes preinstalled in the BIOS of some laptops. If the laptop is lost or stolen and later connected to the internet, LoJack will report the location of the laptop to a server. LoJack is designed to remain on the laptop even if its hard disk drive is erased or replaced.
- Sony BMG. In 2005, Sony installed a rootkit known as XCP (Extended Copy Protection) on music CD’s that it released. When users attempted to play the CD’s through their computer, the rootkit created security vulnerabilities. The intention of the rootkit was to prevent people from copying music off the CD’s, but the rootkit created security holes and hid in the background.
Sony was forced to recall all unsold music CDs and faced multiple class-action lawsuits.
A keylogger records each key that a user presses. It may also take screenshots, activate the webcam, or activate the microphone without the knowledge or consent of the user.
The keylogger reports all data back to a central source or records the data on the computer for further retrieval. Data may be sent via
- Email
- FTP
- Wireless/Bluetooth to a nearby receiver
A keylogger may have legitimate purposes if installed by an employer or law enforcement agency. Some antivirus programs will detect keyloggers created by law enforcement and some will deliberately ignore them.
A keylogger may be used to invade the privacy of another person (stalking) or it may be used for financial gain (the logged data is analysed to obtain online banking passwords, e-mail passwords, etc.).
The keylogger may be introduced into a system through another type of malware such as a virus or trojan.
Whether the keylogger can be detected by an antivirus program depends on where it runs. Keyloggers that run in the operating system kernel or through a hypervisor may be undetectable.
Keyloggers can also be hardware-based
- Keyboard keylogger device (USB device that sits between the keyboard cable and the computer). A keyboard’s circuitry can be covertly modified to include a keylogger.
- Wireless keyboard sniffer (device that can intercept signals between a wireless keyboard and the dongle; this device functions when the connection is not encrypted or where the encryption method can be easily broken)
How to prevent keyloggers
- It is difficult, if not impossible to detect a hardware based keylogger, especially one that is embedded into the device circuitry. Keeping computer hardware physically secure is the best defense.
- The use of multi-factor authentication methods can keep accounts secure even when the usernames and passwords are compromised.
- Most software-based keyloggers are detectable by antivirus programs. Some software-based keyloggers that take advantage of zero-day exploits or that operate on the firmware, kernel, or hypervisor level cannot be detected.
Adware is software that shows advertisements. The advertisements may appear as pop-ups, videos, or audio. Adware may be included in legitimate software programs such as games, music applications, or other applications. Typically, adware is bundled with low-quality applications. The advertisements are also of low quality as most legitimate advertisers do not want to be associated with this type of exploitation.
Adware can also be installed without the user’s consent when introduced as part of a computer virus or trojan.
Adware can hijack legitimate website advertisements. When a user visits a legitimate website, the adware swaps advertisements placed by the website owner with advertisements sold by the adware publisher. Thus, the revenue from the advertisements is diverted to the adware publisher without the knowledge of the user or website owner.
It may be difficult or impossible to remove adware. Adware may spy on a user’s activity or browsing history. The adware publisher may sell this data to market research firms or use it to show the user more relevant advertising.
It is illegal to install or distribute adware without the consent of the user. In addition, the user must have an opportunity to remove the adware. There is no specific anti-adware law, but in the United States Section 5 of the Federal Trade Commission Act prohibits “unfair or deceptive acts”. The Federal Trade Commission (FTC) is empowered to commence civil actions against publishers who distribute adware.
Social engineering is the attempt to use psychological methods to manipulate individuals into providing confidential information or access to systems.
Unlike malware, social engineering relies on human emotion. People fall victim because they have the following feelings
- Wanting to be liked
- Fear
- Wanting to help
- Intimidation
- Familiarity
- Hostility
A good book on social engineering is Social Engineering: The Art of Human Hacking by Christopher Hadnagy.
Why do social engineering attempts work? There are many reasons.
- Authority
- The person on the other end of the phone call/in person acts with authority. People are afraid to challenge those who appear to be in a position of authority (such as members of senior management).
- Authority can be established by confidence, tone of voice, clothing, and/or uniforms.
- People are afraid to challenge authority because of perceived negative consequences (getting fired)
- The consequences do not have to be explicitly stated by the thief. They can be implied, or the user might simply assume what they are based on the alleged authority.
- Social engineering authority attacks can be prevented by enforcing policy against all users, regardless of their position. The company must create a culture where verifying the identity of another person is encouraged, regardless of that person’s position.
- For example, the thief could pretend to be a member of senior management and convince the victim that she could lose her job if she does not comply. The thief could demand that the victim provide him with corporate financial information, or wire money to a third party.
- The person on the other end of the phone call/in person acts with authority. People are afraid to challenge those who appear to be in a position of authority (such as members of senior management).
- Intimidation
- Intimidation uses the threat or idea of negative consequences if the person fails to comply.
- The thief does not have to make any direct threats, but instead may cause the victim to believe that negative consequences will occur (or the victim may assume that negative consequences will occur if they fail to comply).
- For example, the thief could pretend to be a police officer and convince the victim that she will be arrested if she does not comply. The thief demands that the victim disclose sensitive data relevant to an investigation.
- Intimidation uses the threat or idea of negative consequences if the person fails to comply.
- Consensus
- Consensus involves a group-decision.
- If a social engineer is unable to convince a specific person to perform an action, he could attempt to convince others in that person’s social circle. Those other people could convince the victim to proceed.
- For example, the thief could convince the victim that her co-workers completed the same action.
- Consensus involves a group-decision.
- Scarcity
- Scarcity means that something is unavailable or in limited supply.
- If the victim values something that is scarce, they may forgo normal procedures and fall into the trap to obtain that item.
- For example, the victim wants a rare (sold out) toy at Christmas time. The thief convinces her that he can supply the toy if she provides him with her credit card/banking information (which he uses fraudulently). The victim never receives the toy.
- Scarcity means that something is unavailable or in limited supply.
- Familiarity
- The victim feels familiar with the situation and proceeds because nothing seems out of place.
- The thief can convince the victim to focus on ideas that are familiar, by dropping familiar names, projects, or other tasks into the conversation.
- Although the victim does not know the thief, she is led to believe that he is a legitimate co-worker because he has knowledge of the workplace or business.
- The victim feels familiar with the situation and proceeds because nothing seems out of place.
- Trust
- The victim trusts the thief and proceeds with their own free will.
- The victim believes that the person they are talking to or the site that they have visited is legitimate.
- The thief may take time to build this trust, especially with a high-value target. The greater the victim trusts the thief, the more the victim will be willing to do.
- The victim trusts the thief and proceeds with their own free will.
- Urgency
- Urgency is like scarcity
- Urgency builds on the idea that there is a limited time to act.
- People hate losing money more than they hate not making money.
- For example, the victim could be told that money is about to be withdrawn from their bank account and they only have a few minutes to stop it (by providing their banking information to the thief). Normally, the victim would take their time to check that the person they are speaking with is legitimate but bypasses these risk controls because of the urgency.
- Urgency is like scarcity
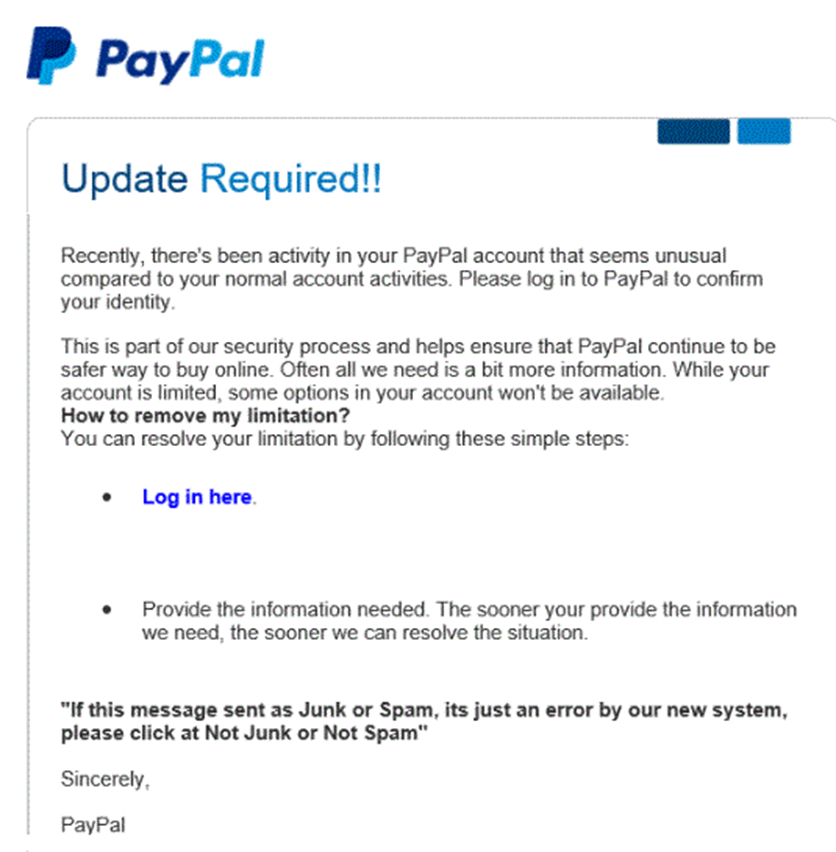
Phishing is the attempt to obtain sensitive data by pretending to be a trusted entity. Phishing usually occurs through e-mail or telephone. Phishing is usually sent as a mass e-mail to thousands or millions of people.
Typically, a user will receive an e-mail asking them to sign in to their bank account or other account (such as PayPal, eBay, Amazon). The e-mail is fake, and the website that the e-mail leads to is fake (but appears to be real).
Typical phishing e-mails will say
- Your account has been compromised and you must log in to correct the issue
- Your account will be suspended if you don’t log in
- You have received a large payment (Interac eTransfer) and you must log in to accept the money
The hacker may register a domain that looks like the legitimate one. For example, the user may register www.paypa1.com instead of www.paypal.com. Or the hacker may register a domain that is completely unrelated to the original website and attach a subdomain that looks like the legitimate site. For example, the hacker registers fakewebsite.com and attaches the “www.paypal” subdomain to it, making www.paypal.com.fakewebsite.com. The users will see the first part of the URL “www.paypal.com” and think they are on a legitimate site, even though the user’s browser went to fakewebsite.com.
How do we prevent phishing?
- Proper user education to identify suspicious e-mails.
- Knowledge that legitimate e-mails from banks and other sites will contain the user’s full name while phishing e-mails will not (unless the sender has access to the user’s data)
- Phishing e-mails and/or websites may (but not always) contain poor grammar or spelling
- Phishing websites will not contain the correct URL. Users should always check that they have visited the correct URL.
- Knowledge that legitimate e-mails from banks and other sites will contain the user’s full name while phishing e-mails will not (unless the sender has access to the user’s data)
- Automated systems that detect and filter phishing e-mails. These systems are built into most web browsers and e-mail systems and verify that the e-mails originated from legitimate sources and that the websites are legitimate.
Spear Phishing is like phishing, but it targets specific groups or people who have lots of money and/or are more likely to respond. The more precise the target, the higher the response rate.
A normal phishing attack could target millions of users. For example,
- A hacker could send a fake e-mail appearing to be from Bank of America to 1,000,000 e-mail addresses
- From those 1,000,000 addresses, only 250,000 might be valid
- The SPAM filter would block 200,000 from those 250,000
- From the 50,000 only 10,000 might have accounts at Bank of America
- 80% of those users might be smart enough to detect the phishing scam, in which case only 2,000 people respond
- The attack is shut down early on (because some users report the scam leading the website to be blacklisted by web browsers), and many subsequent users are warned, so the hackers only collect data from 500 users
- Thus, the success rate is about 0.005%. Although it is low, the return on investment might be high. It may cost the hackers a few hundred dollars to send out the e-mail, but if they are able to collect at least $100 from each user, they could collect $50,000.
In spear phishing, the hackers identify specific customers of Bank of America for example. They may use a list stolen from the bank. The hackers customize the e-mail to include the name and other personally identifying information of each recipient. As a result, the SPAM filter will be less likely to identify the e-mail as SPAM, and the user will be more likely to respond. The hackers send out fewer emails but may collect more money.
Whaling is like Phishing, but targets high-value individuals such as celebrities, CEOs or other executives. Whaling is specifically targeted to the high-value individual. Whaling takes more effort to execute, but the response rate is higher, and the amount of money stolen from each user is higher. Many high-net worth individuals have access to credit cards with high limits.
Another scheme involves a scammer visiting a store such as Best Buy and attempting to illegally purchase expensive electronics in the name of a celebrity on credit. The scammer disappears with the electronics and the store is never paid. The store should have verified that the buyer legitimately represents the celebrity.
How do we prevent whaling?
- Proper user education
- 100% identity verification of the person who is seeking information.
- A high-net worth individual should understand that he is at much higher risk of exploitation either through fraud or extortion schemes. This person should employ people who specialize in detecting and preventing these threats.
Vishing is like Phishing but uses the telephone (VoIP) network. The thieves will place phone calls that appear to come from legitimate entities such as the IRS, a bank, or a credit card company. The thieves will attempt to obtain sensitive data such as credit card numbers or bank account numbers.
Common features
- The scammer will threaten the victim with legal action or arrest if they do not comply
- The scammer will ask the victim to purchase gift cards from a store and send them the numbers
- The scammer will speak with a foreign accent or bad grammar (but not always)
How to Prevent?
- If a user receives a telephone call from somebody who is seeking sensitive information, they should
- Verify that the number is in fact legitimate
- Hang up and call the number back (as caller IDs can be spoofed)
- Verify that the caller will require the information (for example a bank will never ask a client for his/her PIN)
- Provide the required information through the legitimate online website of the purported requester (such as IRS.gov)
- Verify that the number is in fact legitimate
Tailgaiting is an attempt to obtain unauthorized access to a physical facility.
Many offices, industrial facilities, and data centers are controlled via electronic proximity card and/or biometric locks. When a legitimate user unlocks an entrance with their access card and/or biometric lock, an intruder can follow them into the building. Tailgaiting works because
- A person might hold the door open for a person who is walking behind him (doing otherwise might be considered rude)
- A person might not wait to verify that the door closed and locked behind him, and another person might follow him. The door lock might not work properly, in which case the door does not fully close.
When a user deliberately allows another user to follow him through the secure entrance, it is known as piggybacking. An attacker might try to gain access to a secure facility by convincing another user that he is a legitimate employee or vendor and forgot his keycard.
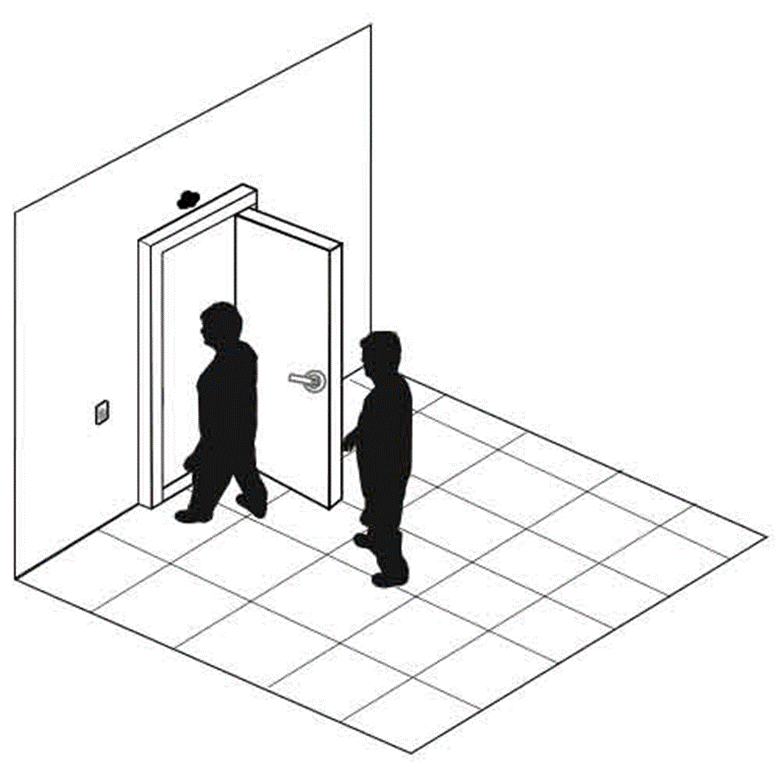
How to prevent
- Proper user education to enforce the use of access cards and prohibit tailgating. Users should know that not holding the door is not considered rude.
- Install a security guard at each entrance or monitor entrances with security cameras
- In more extreme cases, installation of man trap doors might be necessary. A man trap door allows only one person to enter at a time. The man trap door contains cameras with artificial intelligence to detect the number of people inside and permits entry to only one individual at a time.

Shoulder Surfing is when a thief looks over the shoulder of a victim. Shoulder surfing can occur at a computer or at an ATM. The thief may watch the screen or the keyboard. The thief might also watch the reflection of the screen on another surface.
Shoulder surfing happens at offices, in airports, and on public transportation.
How to prevent
- Install shields at ATMs and debit/credit card terminals
- Install privacy screens on computers/laptops.
- If using a laptop on an airplane or other public place, the user should avoid doing anything sensitive and/or be wary of his/her neighbors/surroundings.

